The Ultimate Guide to Hardware Wallets: The Best Hardware Wallets in 2024 and Why You Need One
Mt. Gox.
FTX.
Celsius.
BlockFi.
What do these exchanges have in common?
These were some of the biggest crypto exchanges in the world, trusted to safeguard the assets of their users, and they failed.
Imagine diligently building your crypto portfolio over the course of years. Your BTC & ETH investments are looking promising, and you’ve built an array of altcoins that you plan to hold long-term, anticipating future growth. One day, you log into your exchange account to monitor your investments and strategize your next move, only to be greeted by an empty balance and alarming news headlines.
The exchange you trusted has been hacked, and all your funds have vanished.
Your hard-earned investments, painstakingly accumulated over the years, are now gone, victims of a breach you had no control over.
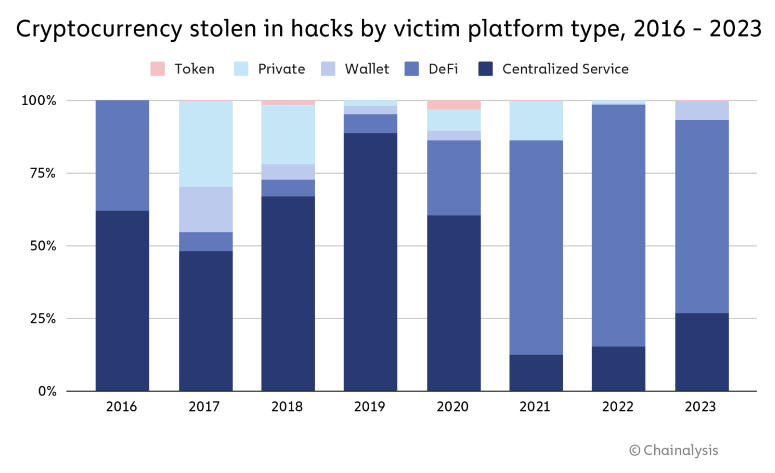
While a minor portfolio might not raise significant concern if held on a reputable exchange, recent events like the FTX collapse serve as a stark reminder of the risks involved. Even the most trusted exchanges can fall victim to hacks or operational failures, potentially resulting in substantial losses for users. The Mt. Gox debacle, the BitGrail saga, and more recent incidents involving Huobi and Kucoin underscore the pervasive threat posed by security breaches and mismanagement in the crypto space.
In successful hack cases, cybercriminals have absconded with millions in various cryptocurrencies, leaving investors grappling with the devastating aftermath. Moreover, the abrupt collapse of platforms like Celsius, BlockFi, and FTX has left countless users locked out of their accounts overnight.
While centralized exchanges have improved their security and increased transparency, any exchange can be hacked at anytime, for a multitude of reasons. A single line of code can be exploited, and there’s the issue of human error – including incompetence, greed, or manipulation. Storing your coins on an exchange, no matter how reputable, means relinquishing control of your private keys. In the event of a security breach or operational failure, there’s little recourse for affected users. As the saying goes, “Not your keys, not your crypto.”
So what’s the best way to prevent a situation like this? How do we ensure your crypto is kept safe, sound and secure? We need a secure crypto wallet.
Types of Wallets
- Software Wallets:
- Desktop Wallets: Installed on a computer, offering a balance of security and convenience.
- Mobile Wallets: Apps on your smartphone that provide easy access but can be vulnerable to malware.
- Web Wallets: Hosted on cloud services, accessible from any device with internet access. These are the least secure as they are always online.
- Paper Wallets: Physical printouts of your private and public keys. Best for those who want to purchase crypto and let it sit for years (which, let’s be honest, has proven to be the best strategy). They are highly secure if stored correctly but are prone to physical damage and loss.
- Brain Wallets: Memorized private keys or recovery phrases. Old school. Specifically helpful for those with a good memory, or in an environment where a written seed phrase cannot be stored. They are secure but risky if forgotten or incorrectly remembered.
While these are all helpful to users in managing funds, we need a hardware wallet (also referred to as a Cold Wallet, or Cold Storage).
What is a Hardware Wallet?
A hardware wallet is a physical device specifically designed to secure your crypto. Unlike software wallets that store private keys on your computer or mobile device, hardware wallets keep your private keys offline, significantly reducing the risk of hacking and theft. These devices usually resemble USB drives and come with robust security features to ensure the safekeeping of your digital assets.
Why Do I Need a Hardware Wallet?
Enhanced Security – Don’t Get Your Crypto Pickpocketed!
What sets hardware wallets apart is their ability to provide robust security while offering convenience and ease of use. By storing private keys offline in a secure element, hardware wallets ensure that even compromised devices cannot compromise the security of your funds.
Each hardware wallet discussed in this guide offers the essential feature of wallet backup, allowing users to restore their funds in case of loss or damage. It’s imperative to adhere to best security practices by backing up your wallet and safeguarding recovery seed phrases.
- Offline Nature: The most significant advantage of hardware wallets is their offline nature. By storing private keys in a secure offline environment, they are virtually immune to online hacking attempts. This level of security is paramount in a world where digital theft is increasingly sophisticated.
- Protection from Malware and Phishing: Software wallets, especially those on mobile devices or web browsers, are vulnerable to malware and phishing attacks. In contrast, hardware wallets require physical access to the device, making remote attacks exceedingly difficult.
- Authentication: They often require physical confirmation of transactions through a button press on the device, adding an extra layer of security.
User Control
- Sole Ownership of Private Keys: When you use a hardware wallet, you retain complete control over your private keys. This is in stark contrast to using wallets hosted by centralized exchanges, where the exchange holds your private keys on your behalf. This means that in the event of an exchange hack or failure, you might lose access to your funds.
- Example: In 2019, the Canadian cryptocurrency exchange QuadrigaCX went offline after its CEO passed away, allegedly being the only person with access to the private keys. Users lost access to $190 million worth of cryptocurrencies because their funds were held in the exchange’s custody.
- Avoiding Third-Party Risk: Centralized exchanges can be tempting for their convenience and ease of use, but they pose significant risks. Besides the risk of hacks, exchanges can also freeze accounts, suspend withdrawals, or even become insolvent, leaving users without access to their funds.
- Example: The Mt. Gox exchange hack in 2014 saw approximately 850,000 Bitcoins (worth around $450 million at the time) stolen from user accounts. Users who stored their funds in personal hardware wallets would have avoided this disaster.
- Exchanges go down all the time. If you ever needed your funds in a crunch, the last thing you’d want to see is this:
Real-World Examples Highlighting the Importance of Hardware Wallets
- Centralized Exchanges Going Under:
- FTX Collapse (2022): One of the most prominent examples in recent years is the collapse of the FTX exchange. The sudden downfall of FTX left countless users unable to withdraw their funds, highlighting the dangers of trusting centralized entities with your assets.
- BlockFi Bankruptcy (2022): BlockFi, a prominent cryptocurrency lending platform, filed for bankruptcy due to its exposure to the FTX collapse. Users who had their assets locked in BlockFi accounts faced significant losses and were unable to access their funds. Those who had transferred their assets to hardware wallets remained unaffected by the bankruptcy.
- Celsius Network Bankruptcy (2022): Celsius Network, a cryptocurrency lending and borrowing platform, also filed for bankruptcy, freezing user accounts and preventing withdrawals. This incident emphasized the risk of keeping assets on centralized platforms. Users with funds in hardware wallets were shielded from these consequences.
- Users Getting Hacked Using Mobile or Browser Extension Wallets:
- MetaMask Phishing Scams: MetaMask, a popular browser extension wallet, has been a frequent target of phishing scams. Users tricked into giving away their seed phrases have lost substantial amounts of crypto. A hardware wallet would have required physical confirmation, stopping such phishing attempts.
- SIM Swapping Attacks: Mobile wallets are vulnerable to SIM swapping, where hackers gain control of a user’s phone number and use it to access two-factor authentication codes. This allows them to take over mobile wallets. Hardware wallets, not relying on such online authentication methods, provide a safer alternative.
In Short…
The importance of a hardware wallet cannot be overstated in the ever-evolving landscape of crypto security. By offering enhanced security, user control, and a reduced risk of human error, hardware wallets provide a robust solution to the vulnerabilities inherent in other types of wallets. As cases of centralized exchanges going under and users getting hacked using mobile or browser extension wallets demonstrate, the peace of mind and security provided by hardware wallets make them an essential tool for anyone serious about safeguarding their digital assets. Investing in a hardware wallet is an effective step toward ensuring that your crypto remains secure and accessible only to you.
In-Depth Comparison of the Top 5 Hardware Wallets
1. Trezor Model T
Company Profile: Trezor is produced by SatoshiLabs, a pioneer in the hardware wallet industry. Founded in 2013, SatoshiLabs is based in the Czech Republic and is known for its innovative approach to crypto security. The company’s main products are the Trezor One, Safe 3 and recently the Safe 5 with a touchscreen, each of which have become synonymous with high-level security and ease of use. Trezor’s open-source philosophy has set it apart in the industry, offering transparency and trust. Although Trezor has had no significant security breaches, the company continually updates its firmware to address any potential vulnerabilities.
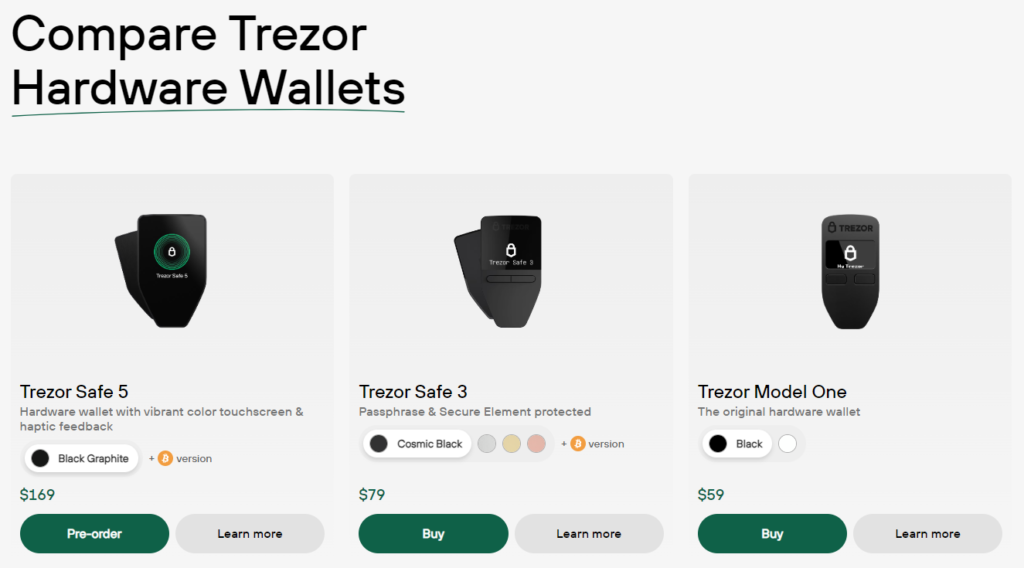
Strengths:
- User Interface: The Trezor Model One features an intuitive and easy to navigate device.
- Open-Source: Transparency in security protocols allows for community audits and trust in the device’s security measures.
- Multi-Currency Support: Supports over 1,600 cryptocurrencies, providing extensive versatility for users.
- Price: At around $60, it’s cheaper than some competitors.
Weaknesses:
- Security Feature: The Model One is missing a Secure Element chip.
- Size: Larger and bulkier than other models, making it less portable.
Features:
- Shamir Backup: A unique way to split the recovery seed into multiple parts, enhancing security and redundancy.
- Passphrase Protection: Adds an extra layer of security to your seed phrase, ensuring your assets are even more secure.
2. Ledger Nano X
Company Profile: Ledger, a French company founded in 2015, is one of the leading names in the crypto hardware wallet market. Known for its Ledger Nano S (now updated to the Nano S Plus) and Ledger Nano X models, the company has built a reputation for innovation and security. Ledger’s main products are designed to provide secure and user-friendly solutions for managing digital assets. Despite a significant data breach in 2020 where customer information was exposed, Ledger has maintained a strong market presence, continually enhancing its security measures and product offerings.
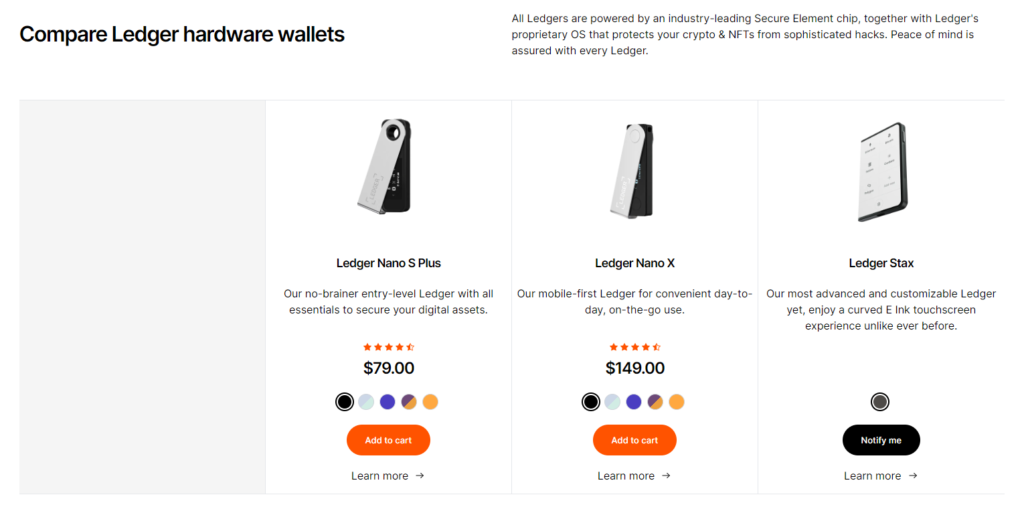
Strengths:
- Bluetooth Connectivity: Allows for wireless transactions, making it convenient to use on the go.
- Multi-Currency Support: Supports over 1,800 cryptocurrencies, catering to a wide range of users.
- Mobile Compatibility: Can be used with both desktop and mobile devices, providing flexibility.
- Price: Priced at $79, it’s on the lower end compared to other options – though for some users, upgrading to the Nano X might be preferred.
Weaknesses:
- Closed-Source: Limited transparency in security protocols, which may concern some users.
- Security Concern: It’s never a good look when a company has a data breach. After a data breach, customers begin to ask where else vulnerabilities may exist. It’s helpful to remember that over 6 million Nanos have been sold, and none have ever been hacked, according to Ledger’s Blog.
Features:
- Large Storage Capacity: Can handle multiple apps simultaneously, accommodating a variety of cryptocurrencies and functions.
- Secure Element Chip: Provides an extra layer of security, protecting private keys and sensitive information.
3. NGRAVE ZERO
Company Profile: NGRAVE is a relatively new entrant in the hardware wallet market, established in 2018. The Belgian company is known for its focus on security, having developed the NGRAVE ZERO in collaboration with the Interuniversity Microelectronics Centre (IMEC) and the Computer Security and Industrial Cryptography (COSIC) research group. NGRAVE’s innovative approach, particularly with its Perfect Key and GRAPHENE systems, has garnered significant attention. Although it lacks the long-term track record of competitors like Trezor and Ledger, NGRAVE’s advanced security features position it as a formidable player in the market. It’s dubbed “The Coldest Wallet”.
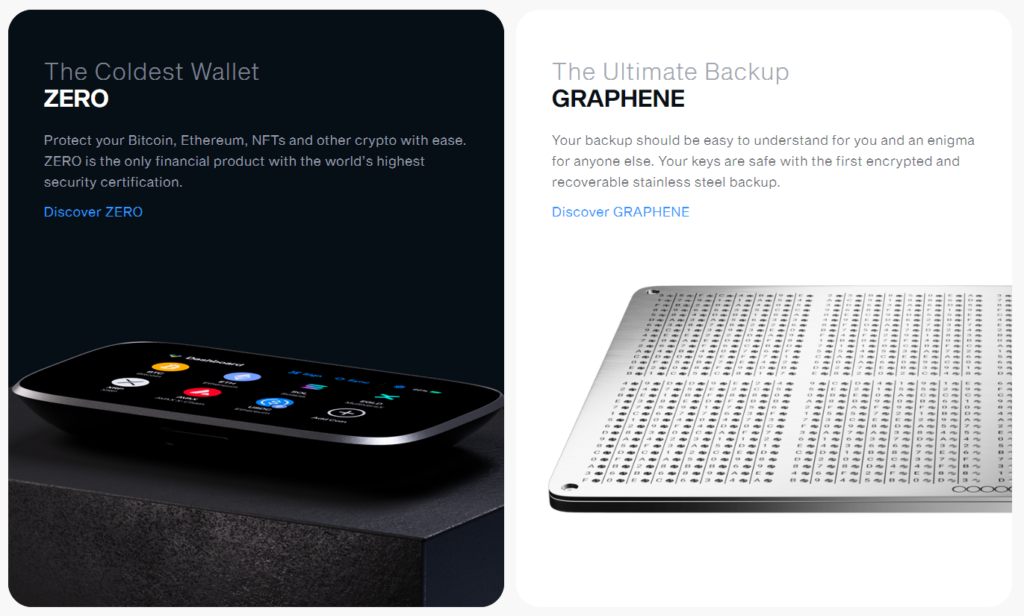
Strengths:
- Air-Gapped: Completely offline, eliminating the risk of remote attacks.
- Perfect Key: Unique private key generation and recovery system that enhances security.
Weaknesses:
- Price: Very expensive at $398, which may be prohibitive for some users (this does not include GRAPHENE, just the ZERO)
- New Entrant: Less proven track record compared to Trezor and Ledger, which might deter some users.
Features:
- IMEC and COSIC Collaboration: Advanced security protocols developed with leading institutions.
- GRAPHENE: Unique recoverable recovery phrase system that offers robust security without third-party risk.
- Biometric Security: This could be considered a strength or a weakness, depending on who you ask.
4. BC Vault
Company Profile: BC Vault is produced by REAL Security, a cybersecurity firm with over 20 years of experience. The company is known for its high-security solutions and has made a significant impact with the ‘Seedless’ BC Vault hardware wallet. REAL Security’s background in cybersecurity lends credibility and trust to the BC Vault, which is marketed as one of the most secure hardware wallets available. BC Vault has not experienced any major security breaches, and its products are designed with long-term durability and advanced security features in mind. They claim to include 1 BTC with each BC Vault, and if you can break the encryption securing it, the BTC is yours. Quite the statement.

Strengths:
- Storage Capacity: Can support up to 2,000 unique wallet addresses, making it suitable for managing multiple assets.
- Long-Term Durability: Uses FeRAM, which can last over 200 years, ensuring longevity and reliability.
Weaknesses:
- Interface: Less intuitive compared to Trezor and Ledger, which may affect user experience.
- Price: Moderately priced at $138, which is higher than some competitors.
- Closed-Source: the REAL team believes with open-source code, malicious actors will have more access to dangerous information.
Features:
- Seedless Recovery: Unique recovery method that does not rely on traditional seed phrases, enhancing security.
- True Random Number Generator: Ensures private keys are unique and secure, providing peace of mind for users.
- Day-to-Day Use: Because this is a ‘vault’ with an emphasis on security measures, this may not be the best storage choice for those looking to access their holdings often.
5. Tangem Wallet
Company Profile: Tangem is a Swiss company specializing in smart card technology. Founded in 2017, Tangem focuses on creating user-friendly and secure hardware wallets. The Tangem Wallet, designed as a credit-card-sized device, is known for its ease of use and durability. Tangem has not faced any significant security breaches and has been independently audited to ensure the integrity and security of its products. The company’s emphasis on eliminating single points of failure and providing a seamless user experience has made Tangem a popular choice among crypto enthusiasts.
Strengths:
- Ease of Use: Setup and transactions are extremely user-friendly, making it accessible for beginners.
- Durability: Card-sized and highly resistant to environmental factors, ensuring longevity and reliability.
Weaknesses:
- Limited Features: Lacks some advanced features of other wallets, which may not meet the needs of advanced users.
- Reliance on Mobile App: Requires a smartphone for operations, which might be inconvenient for some users.
Features:
- NFC Enabled: Allows tap-and-go transactions, providing convenience and ease of use.
- Affordable: Priced at $69 for a 3-card set, making it one of the most budget-friendly options on the market.
What to Do If You Lose Your Wallet or Forget Your Key
Losing your hardware wallet or forgetting your private key can be a stressful experience, but it’s not necessarily the end of the world. Here’s a guide on what to do in such situations:
- If You Lose Your Wallet:
- Recovery Seed: Most hardware wallets come with a recovery seed phrase. This is a sequence of 12, 18, or 24 words that can be used to restore your wallet and access your funds. Ensure that you have securely stored this seed phrase in a safe place.
- Contact Support: Reach out to the wallet manufacturer’s customer support for guidance. They can provide specific instructions based on the model of your wallet.
- Replacement Device: Purchase a new hardware wallet and use the recovery seed phrase to restore your wallet on the new device.
- If You Forget Your Key:
- Recovery Options: Some wallets, like the Trezor Model T with its Shamir Backup, offer advanced recovery options. Utilize these features if available.
- Passphrase Recovery: If your wallet uses a passphrase, ensure you have it written down or securely stored. If you forget the passphrase, you may still be able to access your funds using the recovery seed.
- Professional Help: In extreme cases, you may seek professional data recovery services, but this can be costly and is not always guaranteed to work.
- Preventive Measures:
- Multiple Backups: Keep multiple copies of your recovery seed phrase in different secure locations to mitigate the risk of losing access.
- Hidden Wallets: Use hidden wallets with separate passphrases to add an extra layer of security and redundancy.
- Regular Checks: Periodically check that your recovery seed phrases are accessible and correct.
Conclusion
In the rapidly evolving world of crypto, security is paramount. Hardware wallets offer a robust solution for safeguarding your digital assets against a variety of threats, from hacking and phishing to the collapse of centralized exchanges. While each wallet has its strengths and weaknesses, understanding these differences can help you choose the best hardware wallet for your needs. Whether you prioritize ease of use, advanced security features, or long-term durability, there’s a hardware wallet out there to meet your requirements. Remember, the key to cryptocurrency security is not just choosing the right wallet but also practicing diligent and informed security measures.
This includes measures beyond the hardware wallet – while the technology offers significant protection, it has its limits. In a scenario where an attacker physically obtains both you and your hardware wallet, they could coerce you into revealing your PIN or seed phrases through threats or force (often referred to as a $5 wrench attack). A good friend of mine has talked about Security Through Obscurity. Come up with creative ways to hide your wallet and seed phrases (that you can reliably remember over a longer period of time), and it’s good practice to keep your crypto holdings private.
This is crucial for several reasons:
- Security Risks: Publicly disclosing your crypto holdings can make you a target for criminals. Hackers might attempt to steal your funds through phishing scams or even physical threats.
- Avoiding Scams: Scammers often target individuals they know have significant crypto holdings. By keeping your assets private, you reduce the risk of becoming a victim of fraud or Ponzi schemes.
- Social and Legal Implications: Publicly sharing your wealth can lead to social friction or unwanted attention. It can also attract legal scrutiny, especially in jurisdictions with unclear regulations around crypto.
- Privacy: Crypto is built on the principle of decentralization and personal privacy. Sharing details about your holdings contradicts this principle and exposes you to unnecessary risks.
By keeping your crypto holdings private, you protect your assets and maintain your personal safety, reducing the risk of becoming a target for various forms of attack and fraud.